Nowadays, smartphones and tablet computers are very popular in our everyday lives. Instead of completing the tasks of traditional personal computers, we keep much more personal information in these handheld devices. So it is very critical to deal with the security concerns of them. Here are some tips:
Jailbreaking is the process of removing the limitations on devices running the manufacturers’ standard operating systems through the use of software and hardware exploits. Jailbreaking permits root access to the device operating system hence allowing the download of additional applications, extensions, and themes that are unavailable through the official app stores. The major reason for jailbreaking is to expand the feature set limited by the manufacturers; nevertheless this also exposes your devices to hackers.
As a first line of defense, the screen lock tries to avoid unauthorized access to your device when it is unattended or even stolen. Other screen lock mechanisms (e.g. unlock patterns, numbers only passcode) may have the same function but they are relatively easier to be infiltrated. Examples of screen locks are shown below:
 |
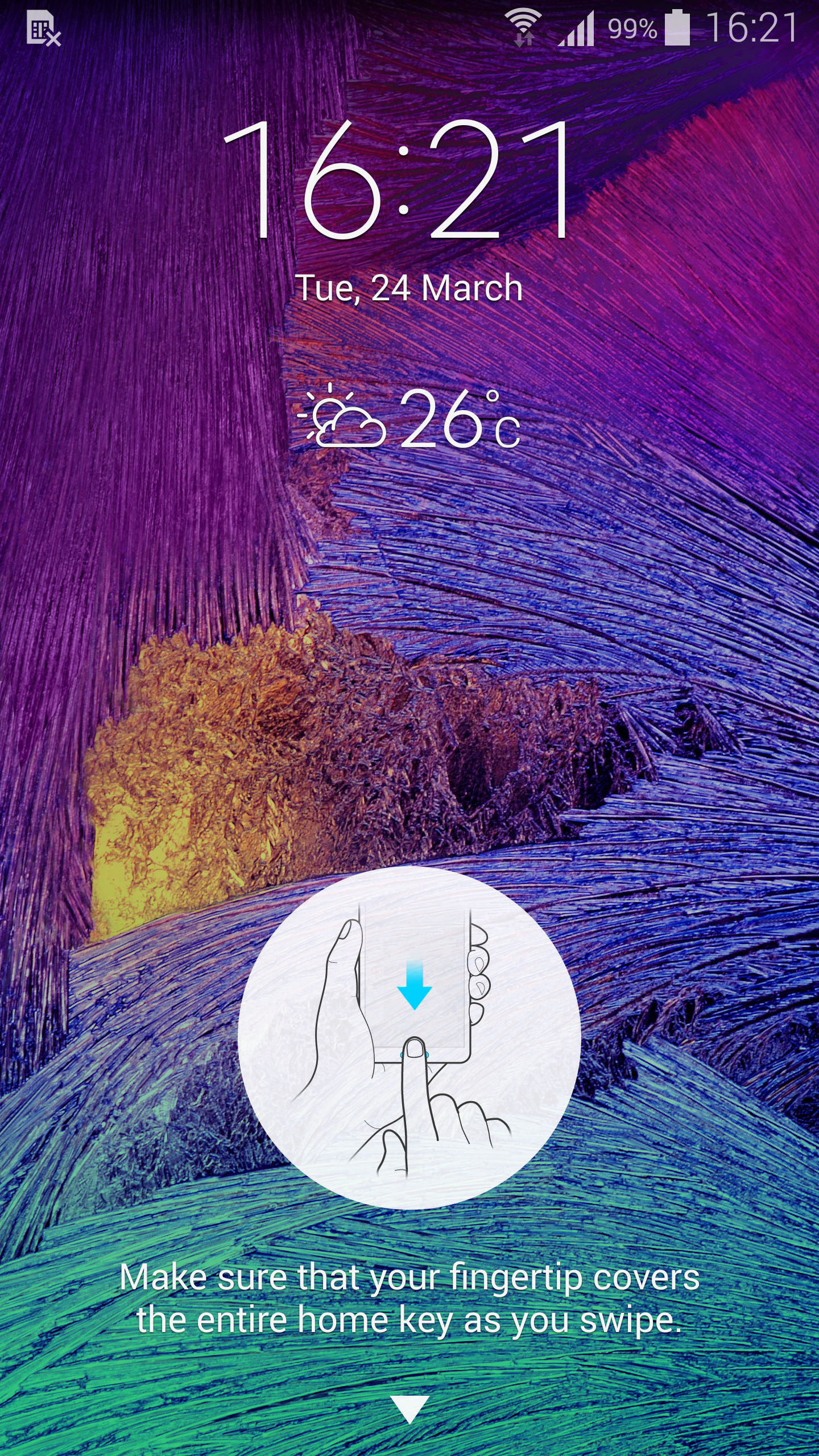 |
When all the information is encrypted, the information inside cannot be accessed, even in case the device is got stolen.
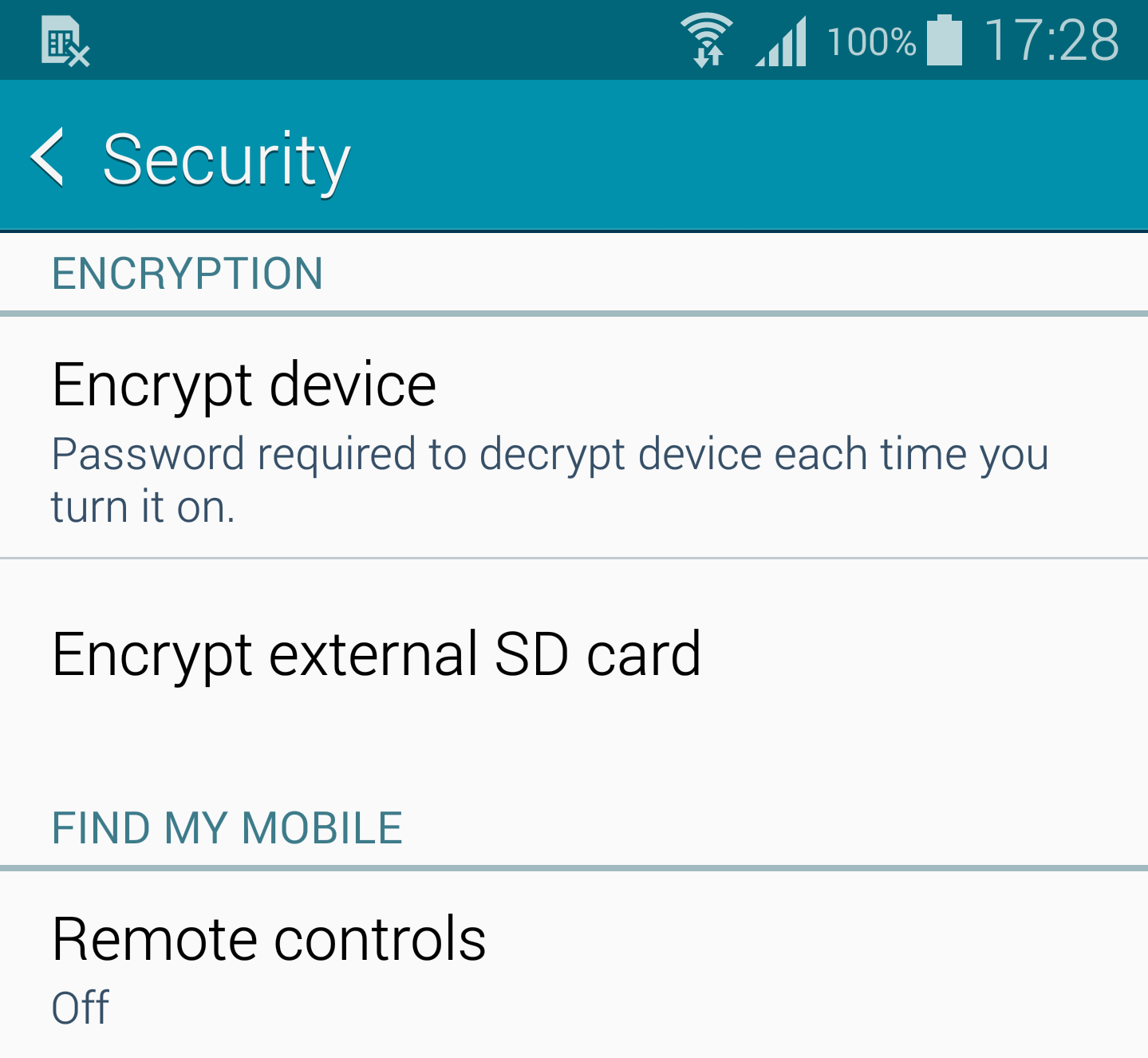 |
When your device is misplaced or got stolen, you can try to locate it remotely, or lock the device from unauthorized access, and even wipe all the data as a last resort.
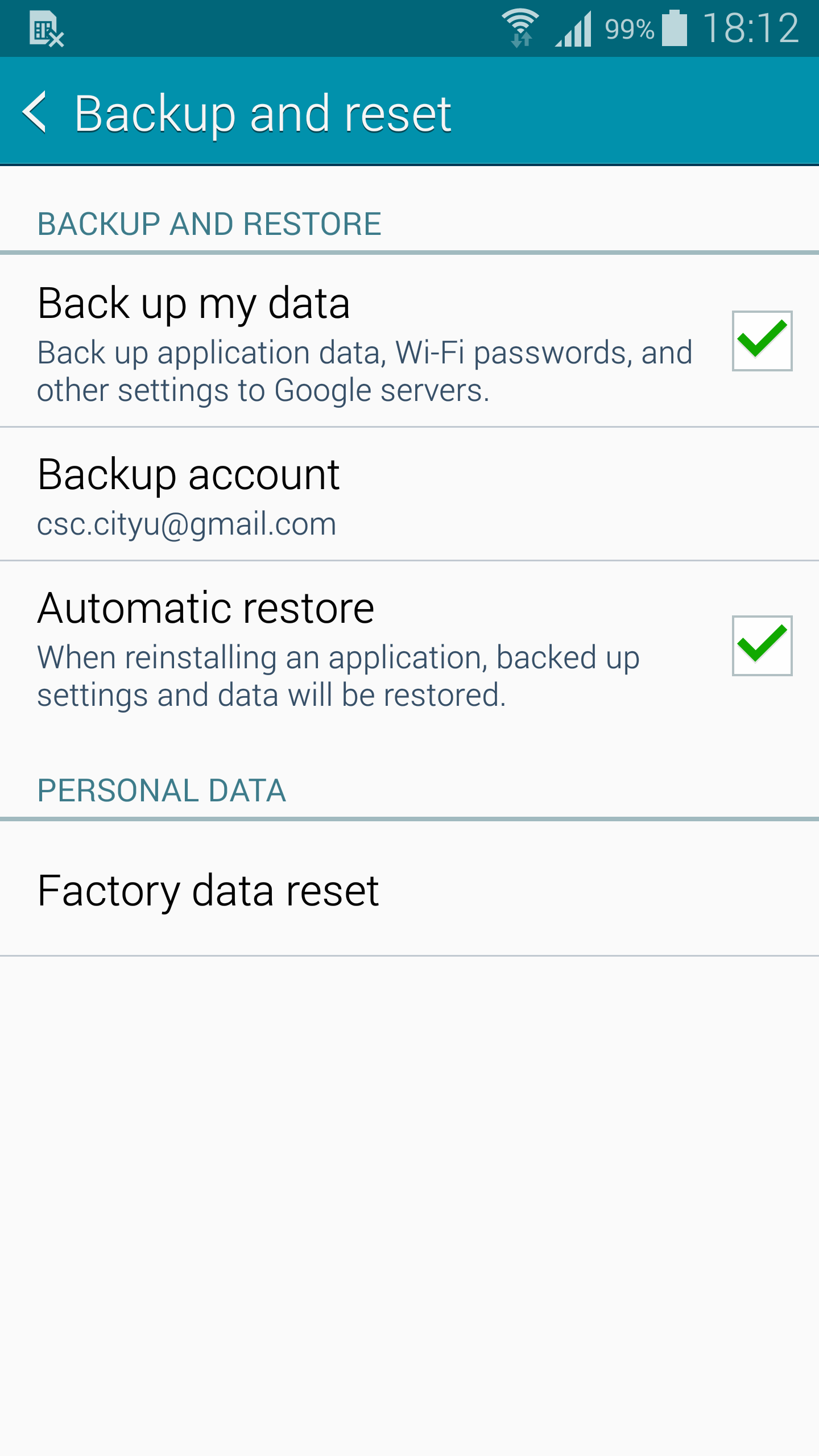
iOS: How to wipe an iOS device remotelyContacts, documents, photos and chat history... etc can be backed up to a PC, removable storage card (if your device supports that), or in the cloud.
For iOS devices: How to back up and restore your contentWhen you are going to download an app, you should conduct some research in advance. Try to check for any reviews, check for its official website from the app store link to make sure if the app is legitimate and safe to be used.

Don’t just keep pressing “OK” or “Accept” when installing an app. Pay attention to the permissions required (e.g. if the app has to access your phone book, camera, or internal storage), make sure you understand why the app has to access such information before accepting its requirements.
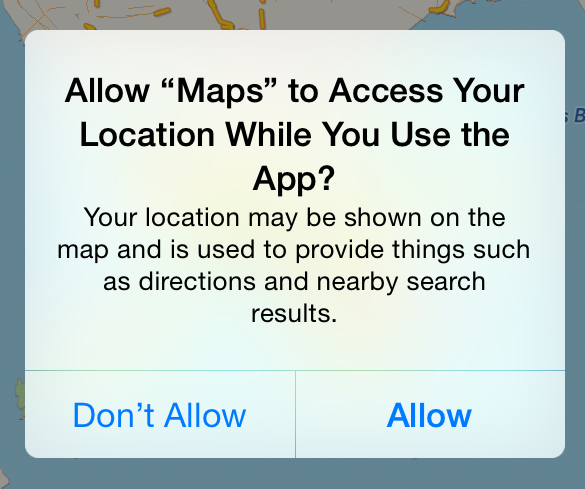 |
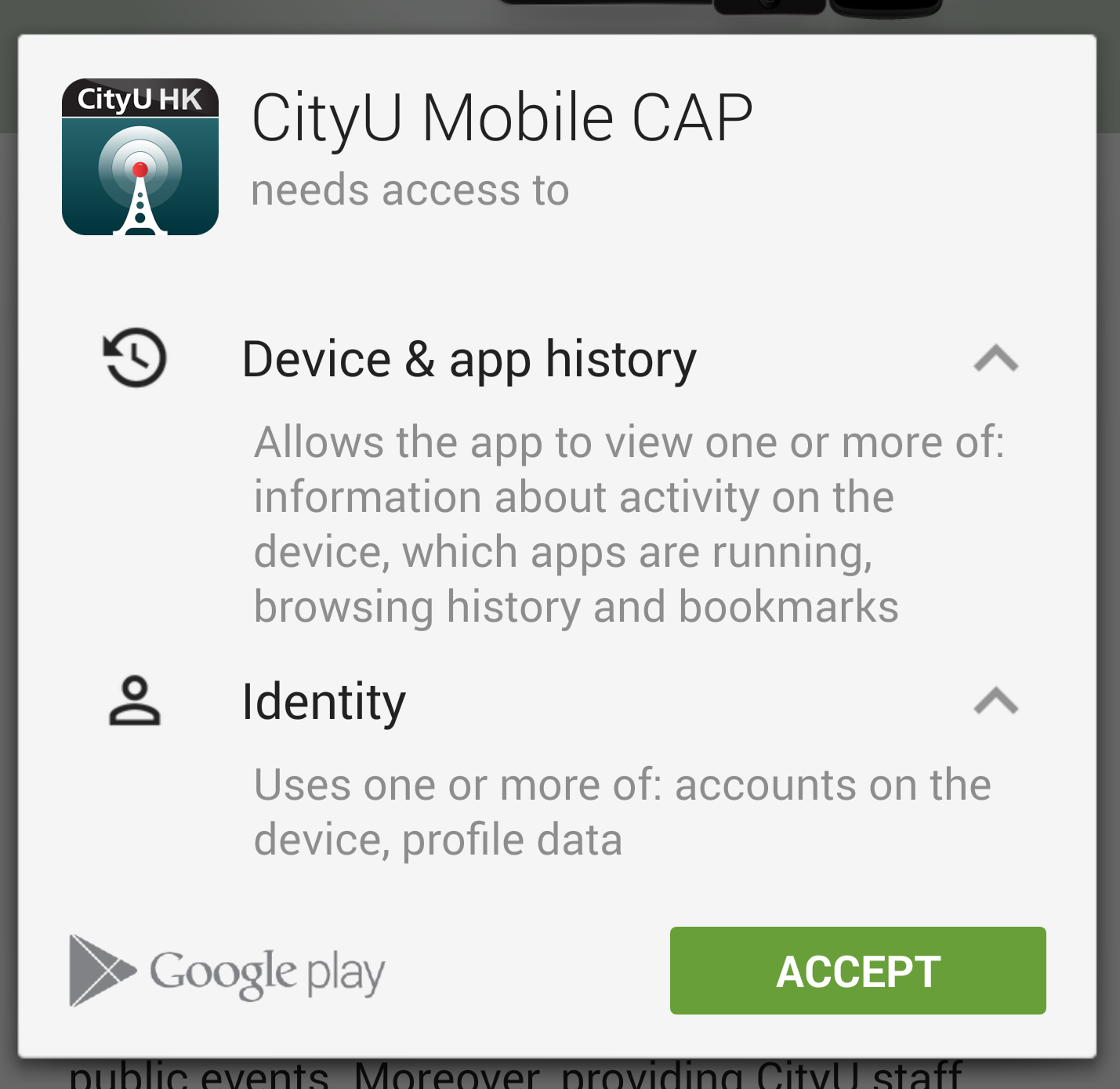 |
By enabling the automatic update function of your device, the operating system software should be updated by the device manufacturer from time to time. An up-to-date OS is more resistance to security threats and vulnerabilities.
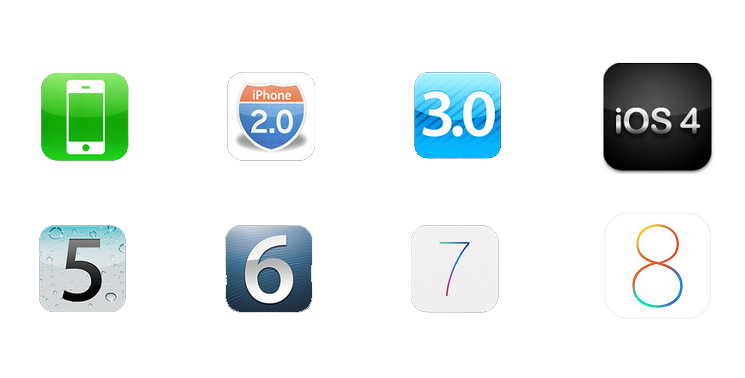 |
 |
As there are many personal information in your device, you should wipe all the data and reset the device to the factory state before dispose or resell it.
 |
When you online through an open WiFi network, beware that all the information you access through this network is not secured. It can be retrieved by the other users on the same WiFi network. Pay extra attention when you are asked for account or login information