I. Background of Firewall
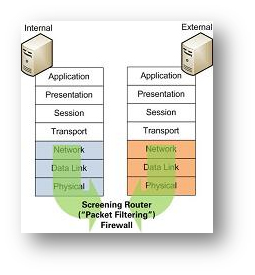
Screening Router
Also known as "Packet Filters", the Screening Router is the first generation of firewall devices built on network routers and operate in first three levels of OSI reference model. The device checks for matches to any of the packet filtering rules pre-configured, and drops or rejects the packet accordingly.
-
Circuit-Level Firewall
 A Circuit-Level Firewall works at the session layer of the OSI model. They monitor TCP handshaking between the packets to determine if a requested session is legitimate.
A Circuit-Level Firewall works at the session layer of the OSI model. They monitor TCP handshaking between the packets to determine if a requested session is legitimate.
A virtual "circuit" is established between the internal terminals and the proxy server. "Network Address Translation" technique is used, where requests from the external networks go through this "circuit" to the proxy server, and the proxy server relays those requests to the external networks after changing the IP addresses of the packets. All packets delivered by the Circuit-Level Firewall are tagged with public IP addresses and the internal private IP addresses are not exposed to potential intruders. There is no way for a remote terminal to determine the internal private IP addresses of the universities.
-
Application-Level Firewall

An Application-Level firewall provides all the Circuit-Level firewall features and also provides extensive packet analysis.Not only does the firewall evaluate IP addresses, it decides whether to drop a packet or send them through based on the application information available in the packet, which stops hackers from hiding information in the packets. Such function is achieved via setting up multiple proxies on a single firewall for difference applications, and examines the data or connection at Application Layer based on tailor-made rule(s) for each application. Because they are application aware, more complex protocols like H.323, SIP and SQL can be handled.
Stateful Inspection Firewall
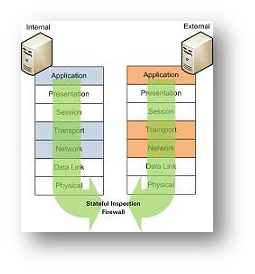
Being the third generation of firewall architecture, Stateful Inspection Firewalls work at multiple layers of OSI reference model, including Network Layer, Transport Layers and Application Layers, and is also known as "Dynamic Packet Filtering" firewalls.
- Inbound and Outbound Filtering - Traffic filtering is the primary and most important function of a firewall. Inbound filtering processes inbound data towards the internal IT environment of the university and rejects any unsecured / malicious content. Outbound filtering can prevent the spread of malware originated from internal hosts and terminates certain types of communication prohibited by the university's information security policy. E.g. Peer-to-Peer, Streaming, etc. This function can also be modified to allow certain external terminals to reach the internal network or for certain data to be released to the external networks.
- Stealth Mode - Firewalls not only block unauthorised requests to the information systems or personal computers within the university, but also avoid sending responses to probing activities committed by hackers, making them in "Stealth Mode" and reducing the exposure to further malicious attacks.
- Privacy and Sensitive Data Protection - Many firewalls now have the ability to block spyware, hijackers, and adware from reaching the university's internal terminals. It prevents authorised leakage of private data or sensitive information of the university and its members.
- Intrusion Detection - Firewalls can detect various intrusion activities via scanning incoming data for signatures of known method, record any suspicious events and notify users when such attacks are recognised. Firewall notifications and logs allow users or IT security staff of the university to timely detect any possible penetration attempts on the university's information systems and resources and prepare corresponding mitigating measures.
References:
http://www.windowsecurity.com/whitepapers/General_Firewall_White_Paper.html
http://www.windowsecurity.com/articles/A_firewall_in_an_IT_system.html
http://windowsupdate.microsoft.com/
http://www.bleepingcomputer.com/tutorials/tutorial60.html