Awareness on Web Site Security
Past hacking and defacement to departmental web sites:
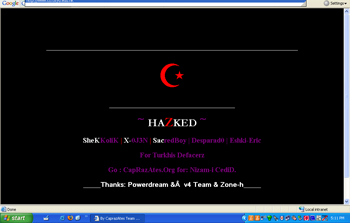
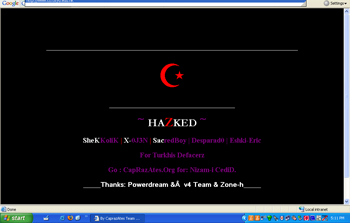
The entire homepage was replaced !!
The center news column was defaced !!

- Web server hi-jacked for further hacking to the other sites
- Web server with e-mail capabilities hi-jacked for e-mail spamming
- Web server contains users' personal information being disclosed
- Web server contains users' account and password or credit card information being stolen and misused
It is a good practice to:
- Take stock of departmental public web sites and services, know their hosting locations and responsible personnel (content & technical).
- For web site that host on departmental server, register your web server with CSC
http://wikisites.cityu.edu.hk/sites/upolicies/itpolicy
To avoid mishaps to your sites, things to discuss with your website developer (colleague, student helper, external contractor):
- Do not install unsolicited software e.g. freeware, shareware.
- Remove old version of program and data.
- Put backup of program and data elsewhere/off-line.
- Separate program source code and executable.
- Jail application to run in least privilege account.
- Use secure protocol HTTPS to transfer sensitive information, e.g. username/password and credit card information.
- Use digital certificate on secured web page.
- Encrypt sensitive information before storing.
- Do not allow web page to write to text file or mdb database file.
- Review web site script to prevent SQL injection that will temper the database, especially via input forms.
- Review web site script to prevent cross-site scripting which foul input with executable codes.
- Obtain proper documentation on web site scripting.
- Sign a non-disclosure agreement on sensitive content.
- Agree on maintenance and warranty period.
- Arrangement on staff turnover.
- How they conduct security testing on the coding and ask for proof.
- Provide a list of software tools that will be used to build the website.
- Don't mix development with the production machine.
Remember your web site needs regular attention!
Things to discuss with your web site host (departmental, external ISP):
- The location of the server is physically secure, access-control is enforced.
- System and network properly protected.
- Apply latest system and security patches timely.
- Have real time anti-virus protection with constant update of virus signature.
- Enable Firewall.
- Disable directory browsing.
- Turn off unnecessary services, functions and features, e.g. SMTP, FTP etc.
- Do not allow directory to be written by web page, everyone or guest.
- Use strong password policy.
- Enable access logging.
- Customize error responses.
- Arrangement of web site and content on retirement of service and server migration.
- List the security measures to be implemented in additional to the forgoing ones.
- Sign non-disclosure agreement.
- Well defined incident handling procedure.
Useful reference on web site security:
IT.ServiceDesk@cityu.edu.hk